OutStack Technologies President & Co-Founder Joshua M. Franklin shares some practical advice for election administrators heading to the DEF CON hacking village in Las Vegas.
First off, DEF CON is two words. Just like, FYI. You’ve probably heard a lot of things about traveling to DEF CON. “You’re going to get hacked.” Not just you, but your whole family. They might even hack your baby. That’s a lot of hype, but there are some basic things that election administrators can do to both protect themselves and get the most out of the conference. And that’s what this post is about—how election administrators can get the most out of DEF CON.
Background on Hacker Summer Camp
DEF CON is a hacking conference. And it’s my favorite. I often describe it as hacker Christmas. You can learn about all your favorite things, stay up late, and catch up with old friends. I’ve gone every year since 2012 and I don’t plan to stop. The Blackhat conference is a separate hacking conference that immediately precedes DEF CON, and is much more corporate and expensive. You'll hear it mentioned a lot. DEF CON is the everyperson's conference with tickets hovering around $300 cash. Only cash. You’ll have to pay for a DEF CON ticket at the door and stand in a long line to get your badge. You cannot enter the conference without your badge and they're quite stringent about it. If the line is insanely long and outside, go get coffee and try again later. Your badge is your receipt, so you'll need to photocopy and submit it with your expense reimbursement request—seriously.
Once you get in, there’s loads to do. There’s a dedicated track for people who are new to the conference and not overly technical called DEF CON 101. Start there. You probably want to visit a few talks in DEF 101 during your down time. It’s best to review the DEF CON agenda on the flight beforehand and highlight the talks you'll want to attend. You’ll probably only plant yourself at a third of what you wanted to see, because the day will take you away in interesting ways!
Other than talks, there’s the main event. What you’re paying to go see: the DEF CON Voting Machine Hacking Village. The Village is a little more nebulous than how it’s portrayed in the news, it’s typically split into two parts: the room with the machines, hackers, and poor hygiene, and the speaking room with fancy people who talk about elections and visit the machine room for 15 minutes for a twitter picture. They both go on concurrently. Last year, there was a third election-related activity setup to teach kids white hat hacking called r00tz. While that is an amazing activity that we as a nation need to focus on, the results kinda got out of hand last year in my opinion.
My former boss and I were actually the second speakers ever at the DEF CON voting machine hacking village. You can watch that video and see me uncomfortably respond to questions. But if you’re going to the village to see a bunch of fancy new voting machines get hacked, don’t hold your breath. The Village has not really had the top of the line newest equipment. I’m not sure that they’ve even had anything that’s ever been certified by the US Election Assistance Commission. Not that it really matters, as the machines in the room have very similar software and hardware versions are at the Village that, if hacked, the attacks would likely port over nicely to the federally certified versions. I plan to take up the efficacy of the the Village in the future.
Practical security advice
Let’s talk about your security. There’s a lot of fear, uncertainty, and doubt (FUD) for norms attending DEF CON. While there’s no hard and fast rule for how to keep yourself safe, here’s what I recommend as a telecommunications and mobile security professional.
- 2FA on all your accounts. Google, Amazon, Facebook, Twitter, everything. SMS 2FA is fine if it’s all that’s available. Check out twofactorauth.org if you’ve never taken a gander. If you don’t go through all your accounts and do this, I hope a judge calls in your next major highly contestable election and orders polls to be kept open for an extra 3 hours, and then the power goes out during the second hour. Then, the ballots fall out of the back of the truck into a sewer drain.
- Pay attention to your passwords. Not all of your services will be allow 2FA. CDT put out a killer field guide to password management targeted towards election administrators.
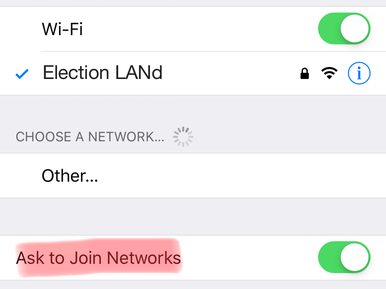
- Turn off WiFi auto connect. Most phones have an option in the WiFi settings to auto connect to networks. Someone is going to be uncool and blast a malicious network and your phone’s going to auto connect. Then they are going to try and break into your phone.
- Don’t bring your phone if it’s rooted or jailbroken. Unless you know exactly what you’re doing with this, you probably will mess this up. Rooting and Jailbreaking often leave your phone in a MUCH less secure state.
- Consider not bringing your work laptop. You can probably get away with just using your phone or tablet for a weekend. If you need to access email on a work laptop, consider bringing a wiped computer with nothing on it.
- Don’t use the DEF CON wireless network. DEF CON provides WiFi for everyone that is a kaleidoscope of danger. Anything you send over the network is being recorded and passed to others for posterity and the wall of sheep.
- Don’t use your hotel’s wireless network. Hackers need a place to sleep and chill at nighttime. They are using the hotel network too and want to share the latest industry tools and scripts with their friends. This is not a recipe for the safety of your devices.
- Use a mobile hotspot if one of your devices needs a network connection. The fact of the matter is, it takes a much more skilled individual to intercept, decrypt (if it’s encrypted, lol), and modify cellular traffic. Hacking WiFi is often the first thing people learn, and there’s devices you can purchase off Amazon that make it easy for kids to mess with you. (You like apples? How ‘bout pineapples?) Pushing all your traffic through the cellular network is more secure.
- Put a lock screen on your phone. I don’t care if you’re using a password, PIN, Android gesture, fingerprint, or facial recognition. Lock your phone somehow. If your PIN is 000000, 111111, 123456 or something similar, somebody is going to guess it. The table below—originally seen here and created by Chris Crowley—contains a list of the most common mobile passcodes. Make sure your lock screen password isn’t on it. People lose their phones in Vegas all the time. It happens. Do this for me.
| 1234 | 1004 | 9999 | 1313 |
| 1111 | 2000 | 3333 | 8888 |
| 0000 | 4444 | 5555 | 4321 |
| 1212 | 2222 | 6666 | 2001 |
| 7777 | 6969 | 1122 | 1010 |
- Update your phone and computer at HOME. Make sure to get the latest security patches and updates for the operating system and all of your applications BEFORE you leave home. Security researchers often release new exploits at Blackhat and DEF CON, and the responsible ones let the affected companies know beforehand. Often the patches that come out right before Blackhat and DEF CON are literally for new stuff that’ being released there. If you can’t update your phone or computer, I would literally not bring it.
- Keep a somewhat low profile. Just like, keep your eyes up. Loose lips sink ships and all that. This will somewhat conflict with the message I give later.
A lot of folks will pressure you to get a VPN on your phone. I don't hate the idea, but in my opinion it's unnecessary if you properly manage your WiFi connection. Reasonable people disagree on this.
¯\_(ツ)_/¯

Getting the Most Out of the Conference
Now that we have all that outta the way, here's additional assignments. First off, take the time to talk to hackers in the village about why they do it. Watch the one kid who sits there all damn day working on one machine. They will likely ask to take the system home at night. They will get there early the next day to continue working. This is what you’re working against. Ask them how they would hack a voting machine. No, they won’t know about elections but this will help you understand the hacking mindset. Educate them on elections. Ask someone about the last thing they hacked or what special project they are pouring their heart into. Learn their story. These people are not your enemy. Many of them would love to help out their local election administrators, but don’t know how.
I also think it’s worth taking the time to go to the other Villages and see how the private sector folks work with the industry there. In the elections world, the economics is completely messed up, and so is how industry, government, and academia all work together. Finally, you’re not alone! Go meet other election administrators and talk about the security and other IT headaches you’re having. I recommend the Lost Policymaker Hacker Summer Camp guide for all newbies. It’s super useful with amazing information for all aspects of the conference.
Thanks to Jerome Lovato for the idea to write this post, and thanks to Dwight Shellman, Jared Marcotte, Kevin Skoglund, and Maurice Turner for their sagacious comments that drastically improved the post's quality.

 Joshua M Franklin
Joshua M Franklin

