In this first piece in our voter registration database auditing series, Solutions Architect John Dziurłaj explains what a voter registration database audit is and why it matters.
Foreign adversaries may not know exactly what is stored in your voter registration database, but as evidenced by the widespread attacks during the 2016 election cycle, they are interested in finding out.
And for good reason. While the Help America Vote Act specifies very narrow requirements for statewide voter registration databases (VRDBs), in reality, they serve as nerve centers of today's election operations.
And as elections modernize, more voter registration services are being offered over the internet. This provides voters with timely information such as registration status, polling locations, and ballot tracking. But this increased access is a double-edged sword, as it also provides attackers with potential pathway into these systems.
Auditing voter registration databases
Even though an ounce of prevention is worth a pound of cure, there are some possibilities we can't guard against. For example, a system may fall victim to a zero day attack, where a previously unknown vulnerability in the technology stack is exploited. If we cannot prevent such attacks, we should at least attempt to detect and respond to them.
By applying auditing techniques to voter registration databases, we can validate that the data stored inside them represents actual ground truth.
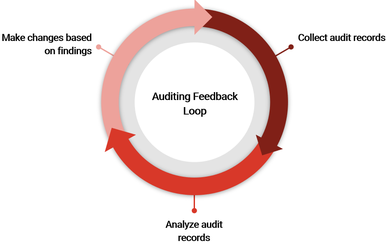
Auditing provides a useful feedback loop to increase the resiliency of our systems. We start by collecting records that are suitable for auditing database activity. Those records are then analyzed to determine if they contain any items of interest. Then investigation occurs and findings are disseminated. Finally, changes are made based on the findings to resolve the issues identified.
Building the audit trail
Before we can audit our systems, we must establish what we mean to audit. We do this by identifying the datasets whose modification should be auditable, i.e. data that is critical to the conduct of the election. This might include:
- Voters’ names, addresses, identification, and eligibility information
- Polling location information
- Contest and candidate information
- Among others.
The audit trail should capture who changed the identified datasets, the nature of the change, and when the change occurred. For personally identifiable information (PII), we may want to know who accessed the information as well.
You might be tempted to include every traceable piece of information in your audit trail. Don’t. It will produce too much noise and you’ll quickly run out of storage. Information systems are complex. A single logical transaction may span dozens of systems, each serving a particular purpose. Additionally, valuable insights may get lost in the deluge.
For auditing to work, we need to track each voter registration transaction as it passes through each of these systems. Correlating transactions is usually as simple as adding a unique identifier that follows the transaction through its lifecycle. When these logs are centralized via a Security Information Event Management (SIEM) system, a fuller picture emerges. For example, a frontend system’s log may include the network information, such as internet protocol (IP) address, while the logs of another system includes details about modifications to the voter record.
Trusting the audit trail
For audits to be meaningful the audit trail must be trustworthy. A trustworthy audit trail will be stored securely with effective controls to restrict its access. Using a centralized storage location for audit data, such as that provided by a SIEM system is ideal. An audit trail must be continuously maintained. Restrict those who have privileges to maintain, and delete the audit trail to a select few, with strong accountability.
Summary
An audit trail is a prerequisite to performing the audit itself. From an information security perspective, audit trails help to provide integrity for systems and data. Integrity one third of the confidentiality, integrity, and availability triad. In a future blog post, we’ll discuss methodologies to performing audits using our audit trail.
Further reading
Once you’re done reading, check out part two about methods of performing a voter registration database audit and part three about the data in a voter registration database, how to identify what's critical, and the importance of metadata.
- https://opensource.com/article/18/9/distributed-tracing-microservices-world
- https://www.cisecurity.org/elections-resources/
- https://github.com/usnistgov/ElectionEventLogging
- https://electionupdates.caltech.edu/2019/05/13/how-to-avoid-an-election-meltdown-in-2020-improve-voter-registration-database-security-and-monitoring/

 John Dziurłaj
John Dziurłaj

